Artificial intelligence is reshaping accounting workflows. Automation speeds reconciliation, invoice processing, and reporting. The same technology also introduces a new category of fraud that many firms have not yet prepared for.
AI tools can generate convincing invoices, vendor profiles, and transaction histories. A fabricated supplier can appear legitimate with a website, email trail, payment instructions, and multiple invoice cycles.
Traditional fraud detection focused on manual manipulation or internal theft. The next phase involves synthetic financial activity created with automated tools.
Bookkeepers and CPAs sit closest to the ledger. Their transaction-level visibility makes them the first line of defense.
This guide explains how AI-generated fraud appears inside accounting systems and how professionals can detect it through bookkeeping signals.
The New Type of Financial Fraud
AI tools can produce:
- Automated invoice generation
- Vendor identity creation
- Fabricated purchase histories
- Realistic payment schedules
- Email conversations confirming transactions
A small business might receive dozens of legitimate invoices every month. Adding a fraudulent vendor inside that stream is easier than ever.
The fraudster’s goal is not large one-time theft. Instead, repeated smaller payments move unnoticed through the ledger.
This makes bookkeeping review extremely important.
Why Traditional Fraud Controls Fail
Most accounting controls rely on documentation.
Fraudsters now generate documentation instantly.
An invoice may include:
- Professional branding
- Purchase order reference
- Tax ID
- Payment instructions
- Digital signature
Everything appears legitimate.
Bookkeeping data becomes the most reliable evidence because financial behavior patterns are harder to fake consistently.
Ledger Signals That Reveal AI Fraud
Fraudulent financial activity often leaves subtle patterns inside accounting records.
1. Transaction Timing Uniformity
AI generated invoices frequently follow predictable timing.
Example pattern:
- Invoice every 30 days exactly
- Identical posting times
- Consistent payment intervals
Real vendors produce irregular billing cycles.
2. Repetitive Invoice Amounts
Machine generated invoices tend to repeat specific price points.
Bookkeepers may notice:
- $4,950 recurring monthly
- $2,750 repeated across invoices
- Rounded totals lacking variation
Real vendor billing usually fluctuates slightly due to taxes, services, or adjustments.
3. Vendor Activity Concentration
AI fraud often focuses activity into a narrow time window.
For example:
- New vendor appears suddenly
- Invoices appear frequently within 3 months
- Then activity disappears
This pattern often indicates short-term extraction.
4. Email Domain Patterns
Fraudulent vendors frequently use:
- Recently created domains
- Free email providers
- Minimal digital footprint
Cross-checking vendor domains reveals suspicious activity.

Reconciliation Red Flags
Bank reconciliation can reveal discrepancies that invoices alone cannot expose.
Key indicators include:
Repeated Payment Destination
Multiple vendors paying into the same bank account may indicate fraud.
Payment Splitting
A fraudulent invoice might be divided into multiple smaller payments to bypass approval thresholds.
Sequential Invoice Numbers
AI generated invoices sometimes produce overly neat sequences.
Example:
INV-1001
INV-1002
INV-1003
Legitimate vendors often show irregular numbering due to multiple clients.
Vendor Verification Framework for Bookkeepers
Bookkeeping teams can create a lightweight verification system without slowing operations.
Step 1: Vendor Identity Check
- Search business registration
- Review company website age
- Confirm domain registration date
Step 2: Payment Consistency Review
Analyze vendor payments for:
- consistent amounts
- predictable intervals
- unusual billing cycles
Step 3: Ledger Pattern Analysis
Compare vendor activity with:
- industry billing norms
- internal expense patterns
- historical spending data
Technology That Helps Detect Fraud
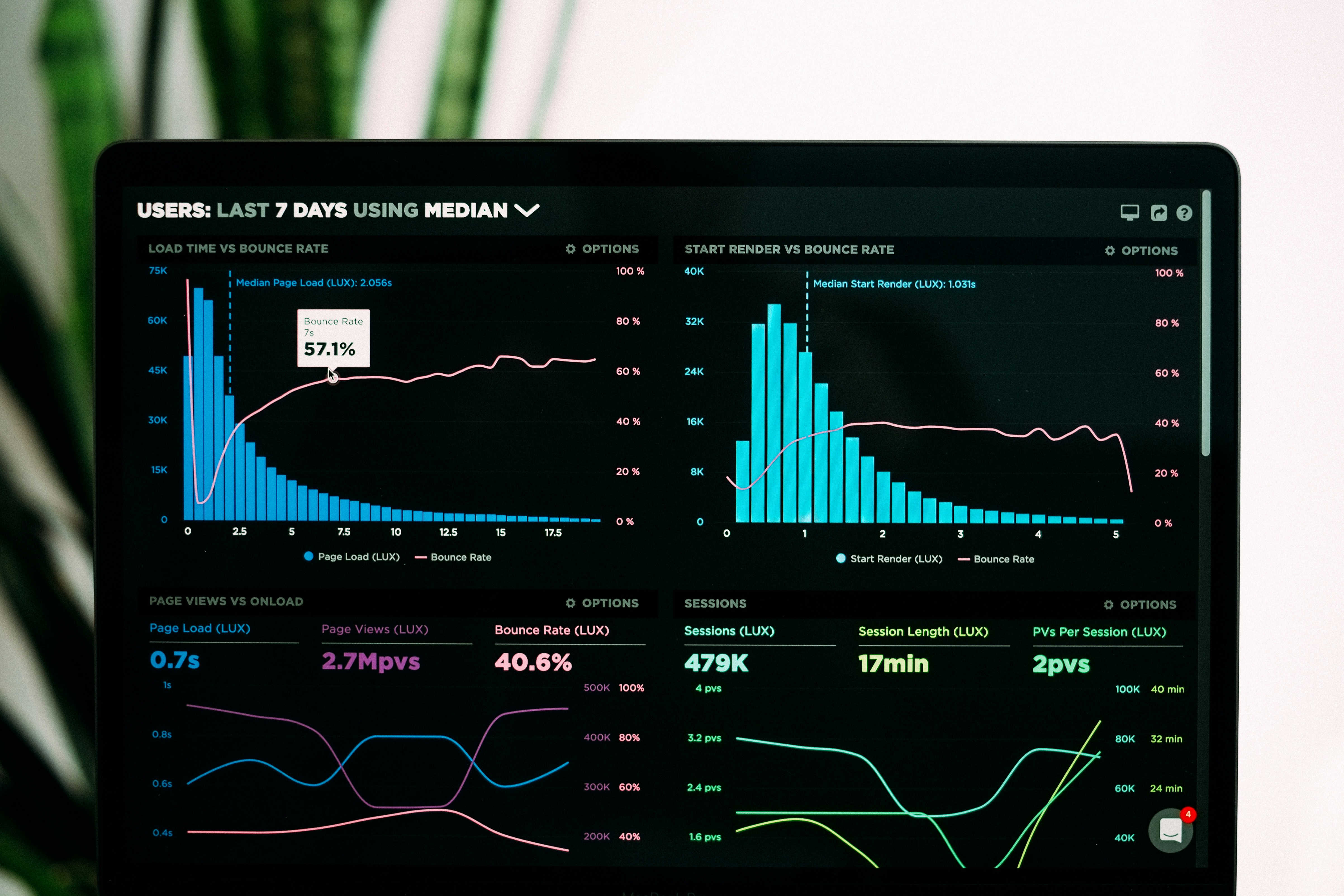
CPAs and bookkeeping firms increasingly use analytics tools to detect irregular patterns.
Examples include:
- transaction clustering
- invoice duplication detection
- vendor anomaly scoring
- expense pattern modeling
These tools analyze thousands of ledger entries quickly.
Human review remains critical because accounting context matters.

Internal Controls Every Firm Should Add
Several safeguards reduce exposure to synthetic financial fraud.
Dual Vendor Approval
Every new vendor requires approval from two people.
Invoice Threshold Alerts
Automated alerts trigger when:
- a vendor reaches spending limits
- billing frequency increases suddenly
Quarterly Vendor Review
Every active vendor should undergo periodic validation.
The Role of Bookkeepers in Fraud Prevention
Bookkeepers see financial activity before auditors, executives, or regulators.
This position allows early detection.
Many fraud cases begin with small irregularities:
- duplicate vendor entries
- minor invoice discrepancies
- strange payment patterns
Attention to these signals prevents larger losses.
What the Next 5 Years Look Like
AI will continue influencing financial operations.
Three trends are already emerging:
- automated invoice creation tools
- synthetic vendor ecosystems
- machine generated payment workflows
Accounting professionals must adapt detection techniques accordingly.
Bookkeeping no longer focuses only on recording transactions.
Pattern analysis and anomaly recognition will become core skills.
Final Thoughts
AI generated financial fraud introduces new risks that traditional documentation checks cannot fully detect.
The ledger still tells the truth.
CPAs and bookkeepers who analyze transaction behavior, vendor patterns, and reconciliation signals will detect fraudulent activity early.
As financial systems grow more automated, bookkeeping expertise becomes even more valuable.
Accurate records are not just about compliance. They reveal the hidden signals that protect businesses from emerging threats.